GeBBS has provided phenominal service to us. We are very impressed with GeBBS’ capability. During COVID, we had to ramp up very quickly and GeBBS was with us every step of the way. I also appreciate the attention to detail and the sense of urgency when we come to them with a problem.
Future of Healthcare
Technology-enabled Revenue Cycle Management and Risk Adjustment solutions for better financial outcomes.
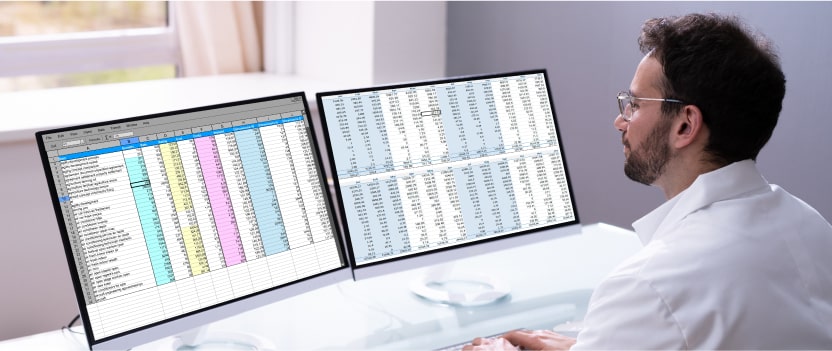
Analytics and Insights That Drive Change
Unlock the value of your data to bring meaningful insights for smart decision-making through our integrated analytics platform.
.
Data Analytics
GeBBS’ insightful data analytics platform and intuitive user interface provide you with relevant reports and powerful visualizations, which help you recognize key focus areas and make quicker decisions.
.
Robotic Process Automation
GeBBS’ certified RPA professionals help you recognize automation opportunities, develop reusable frameworks and BOTs, and develop outcome-driven RPA strategies.
.
Business Process Modelling
Our BPM automation solutions support you throughout the automation process, from identification and conceptualization to execution and process optimization.
.
Artificial Intelligence
GeBBS’ award-winning iCode technology leverages AI, ML, and NLP to enhance medical coding and auditing workflows, improve RAF scores and HCC coding, and optimize your RCM.
Leader in RCM Solutions
GeBBS Named as “Leader” in Everest Group Revenue Cycle Management (RCM) Operations PEAK Matrix® Assessment 2023

GeBBS named to Inc. 5000 list for thirteenth consecutive year
Impact That Drives Performance

Healthcare Technology
How Can We Help You?
HIM Solutions
HIM Solutions
- Cash flow problems
- Errors in Coding
- Inaccurate RAF Scores
- Increase in denials
Patient Contact Solutions
- High eligibility related denials
- Inconsistency in obtaining Authorization
- Inconsistency in tracking POS collections
- Incorrect patient statements
- Rejections and denials
- Untimely followup on patient balances
Extended Business Office
- Compliance issues with Payers
- High AR in 90+ Aging bucket
- High claim rejections
- Higher unbilled claims
- Incomplete resolution
- Reconciliation of payment batches
- Refunds not processed
- Untimely follow-up on underpaid claims
Risk Adjustment
Risk Adjustment
- Deletions of diagnosis
- Errors in Coding
- High acquisition cost
- Inaccurate RAF Scores
- Increased provider abrasion
Compliant with


Over 150 Healthcare Organizations
Partner with GeBBS
Our long-standing evangelists can tell you more

X
Craig A. Adkins
VP Rev Cycle Management, Advanced MD
GeBBS Healthcare Solutions has been our business partner for almost 3 years. They are a very proactive, innovative organization; always looking for ways to improve the revenue cycle. Their management team is responsive, they follow through on their commitments. They are also a very honest and transparent organization, which of course, is very valuable to us.
00:36

X
Michael Weed
SVP of Financial Operations
“Our relationship with GeBBS Healthcare Solutions has been great. They are very attentive to customer service and to what clients ask for. GeBBS Healthcare Solutions is very flexible. GeBBS is also super receptive to feedback we give them about processes. They are open to making course corrections. I really enjoy working with members of the leadership team. They are very easy to work with, and they are eager to give feedback about strategy. We always want someone to point out our blind spots and ways we can improve. GeBBS Healthcare Solutions is willing and open to that. That is a plus.”
X
Shivani Vaid
Vendor Relations Manager
“My experience working with GeBBS solutions has been very positive. The staff and management represent our solutions in the most professional manner possible, while providing us with great recoveries. Over this short period of time, GeBBS has proven to be very dependable and has leveraged their knowledge and resources to supplement our needs very effectively. Their understanding of our systems, practices, patients and staff has created a team environment that has been invaluable to our success. What started as one project has grown into multiple projects due to their ability to be flexible and exceed expectations. It has been a true partnership. I am pleased to highly recommend GeBBS solutions to all.”

X
Brandi Cunliffe
National Coding Director
“The GeBBS team provides timely communication and their responsiveness to our concerns or feedback is much appreciated! I appreciate the weekly check-in calls, their team offers a positive, informative update each week! The GeBBS team sends daily and monthly updates and informative dashboards, these have very helpful to our team in identifying concerns or trends with our clinician documentation.”

X
JoAnn Yohn
Vice President, Revenue Cycle, Kettering Health Network
“We were looking for a company that had both expertise in HIM consulting and compliance auditing; GeBBS Healthcare Solutions filled both of those requirements. Our team is excited to begin using the iCode Assurance tool to improve our coding quality program through improved workflow and data analytics,”

X
Andrew Christman
GM/SVP, Performance Solutions at Continuum Health
“We have been very pleased with the results of our partnership with GeBBS, GeBBS has delivered a highly skilled professional staff using robust processes, proprietary workflow engines, and world-class infrastructure. This has made them a strong partner for us.”

X
Danny Claycomb
Senior Vice President at BioScrip Inc.
“We decided to partner with GeBBS due to their overall experience in Revenue Cycle Management and optimization along with their ability to provide additional valuable workflow software and consulting services to our organization”

X
Sheldon Pink
Senior Vice President, Revenue Cycle Management at Prospect Medical Holdings
“Prospect selected GeBBS because of the depth of their experience, robust processes, and proprietary technology. They are the ideal partner for us”

X
Laurie Weyerstrass
Director of Coding at Lee Health
“We are excited to be working with GeBBS. We selected iCode Assurance because of its enhanced Audit workflow and operations management functionality along with its Claims data aggregation capability. Our team looks forward to using this tool to enhance our coding quality program through improved workflow and data analytics.”
X
Michael Christiano
Director of HIM at St. Anthony Hospital
“Saint Anthony Hospital selected GeBBS because of the depth of their coding and compliance audit expertise in addition to their robust processes and proprietary technology. They are the ideal partner for us. Partnering with GeBBS will allow us to focus on our mission to promote health and provide quality care to patients and families of all faiths”.
Opportunities
to Make an Impact Are Endless
Insights
Insights
News
Blog
Insights
Removing Redundancies from Healthcare RCM with Robotic Process Automation
The creation and development of robotic process automation (RPA) has had a tremendous impact on various industries over the last few years. While
Norwegian American Hospital Saves Over 40% With Strategic HIM Outsourcing
GeBBS audited and developed a comprehensive cost-effective, high quality flexible coding solution. Challenge Clients suffered from a backlog
ABCs of Coding Denials: Avoidable, Burdensome, and Costly
Achieving Business Objectives with Effective Coding & Preventable Denial Strategies I. IntroductionDenials are a leading source of revenue
News
- GeBBS Healthcare Solutions
- 169 Reads
- 45 Shares
- GeBBS Healthcare Solutions
- 199 Reads
- 145 Shares
- GeBBS Healthcare Solutions
- 125 Reads
- 45 Shares
- GeBBS Healthcare Solutions
- 162 Reads
- 90 Shares
Blog
- Revenue Cycle Management
- 20 Reads
- 5 Shares
- Revenue Cycle Management
- 120 Reads
- 50 Shares
- Revenue Cycle Management
- 113 Reads
- 96 Shares
News
GeBBS Education Series is Here!
Register for free and embark on a journey toward professional growth with GeBBS!